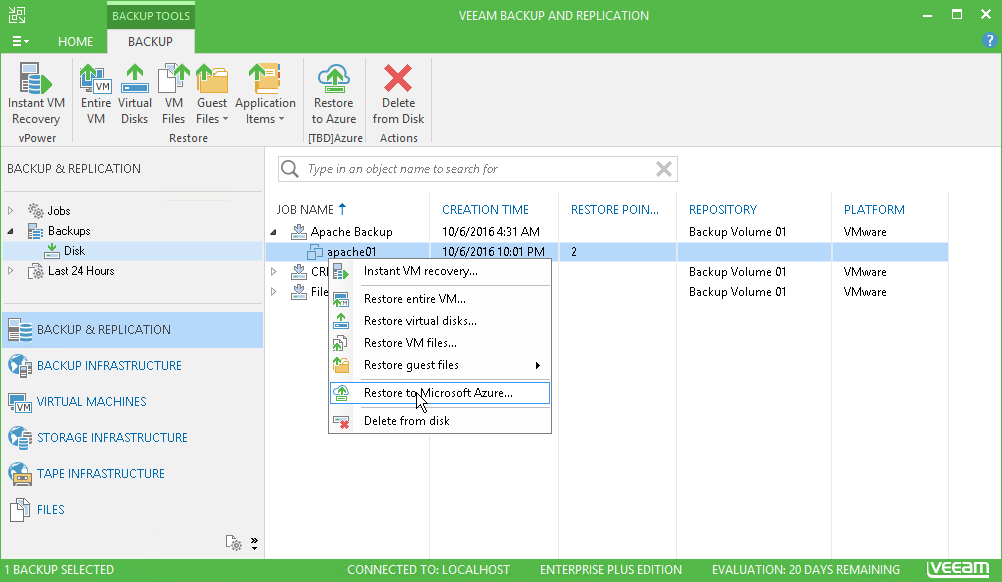
One of the main principles of GDPR is the way in which personal data is processed, this means we must consider things like risk analysis, organisational policies, physical and technical measures. Later in the post I am going to touch on pseudonymisation and encryption and how these can be used to assist the measures to becoming compliant. The measures must ensure “confidentiality, integrity and availability” of systems, services and personal data. My favourite is there must be the ability to restore access and availability to personal data in a timely manner in the event of a physical or a technical incident. Does this mean the backup and replication choice will no longer be last on the list? You also need to ensure that you have appropriate processes in place to test the effectiveness of your measures and undertake any required improvements.
That’s some of the things from a security perspective that should be in place but what if something does get breached and data could have got out of the business. Then you must report any data and security breaches to the information commissioner. This is new as this was a choice from the company if they felt it required by themselves to report. It is not mandatory.
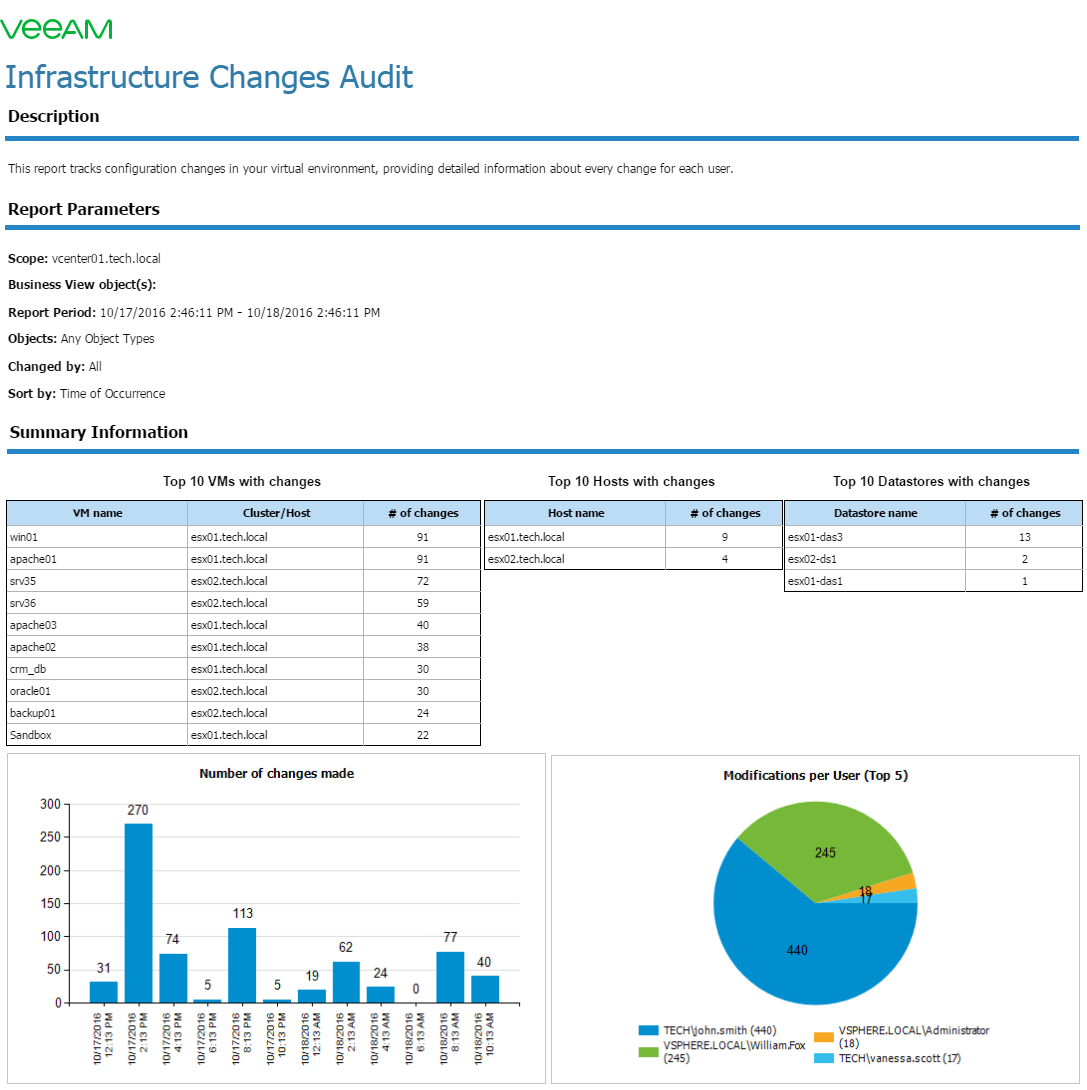
Now we have the overview, I think you will agree it’s going to mean for a huge review for a lot of businesses to understand the way their systems work as well as their employees.

Data Minimisation
Another area that I feel this is going to highlight is the security of systems. Often overlooked or its been the cutting corners for getting things done quicker. GDPR will mean a much stronger focus on technical security, this is going to introduce the use of encryption and having to make sure those security patches are installed on those workloads.
As well as Encryption, pseudonymisation will also be another technique where businesses will have to explore. Pseudonymisation is a technique that allows to replace some of the identifiers with fictitious entries to protect people’s data privacy.
Quote from WikiPedia:
“Pseudonymisation enhances privacy by replacing most identifying fields within a data record by one or more artificial identifiers, or pseudonyms. There can be a single pseudonym for a collection of replaced fields or a pseudonym per replaced field.”
Road Warriors
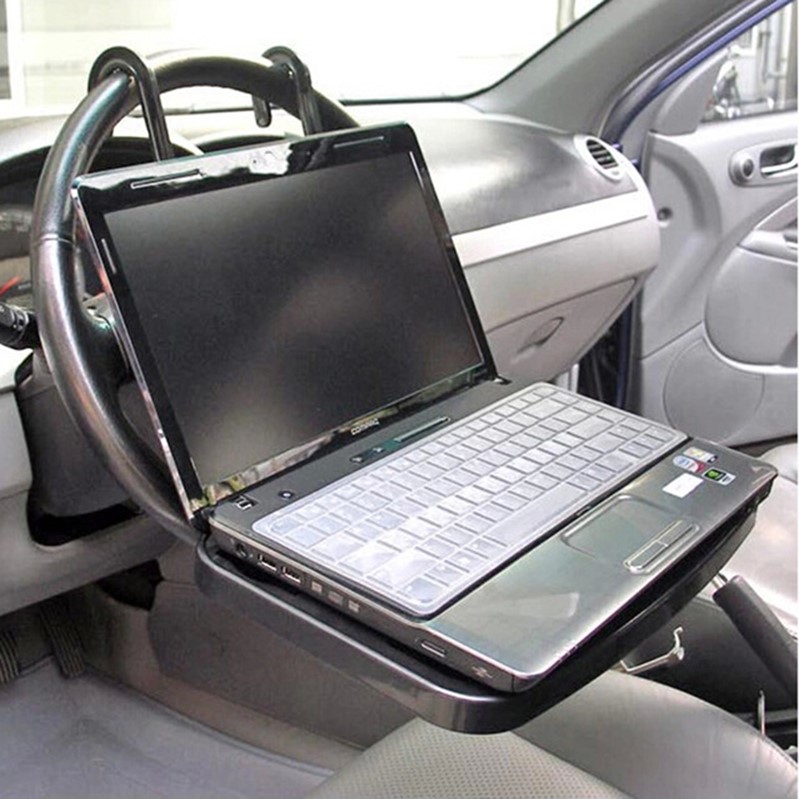
Many of us carry laptops and other mobile devices around with us on a daily basis, the majority of these devices actually contain some work content. How is this affected? Well it comes down to that review of process and directive from the data protection officer. There will be a requirement as there is today but with more of a highlight on making sure staff members are reliable when taking personal data and business data offsite on these devices. Device encryption is one of the areas I can quickly see being the easy tick here but I am sure there are more options around this like remote workers with thin clients on the road. Because this could also put data at risk of exposure and failure to ensure these points could expose businesses to a fine.
