In this episode I hosted my good friend Paul Stringfellow. (Twitter @TechStringy) a Technical Director of a long established UK based IT consultancy, Gardner Systems plc. Michael and Paul talk about the topical threat of Ransomware and the upcoming General Data Protection Regulation (GDPR)
You can find the recording here.
We covered a very topical subject here in the UK regarding GDPR and how come next summer every business is going to have to adhere to these new regulations or face some heavy fines. First of all here is the opening introduction paragraph from the Information Commisioners Office (ICO) website.
“This overview highlights the key themes of the General Data Protection Regulation (GDPR) to help organisations understand the new legal framework in the EU. It explains the similarities with the existing UK Data Protection Act 1998 (DPA), and describes some of the new and different requirements. It is for those who have day-to-day responsibility for data protection.”
The fundamental change and awareness here is when it comes to your data you need to know what data you can keep, how long you can keep it for and what data you must not keep in your possession. This pertains to your production data but also comes into your data protection strategy.
From a Veeam perspective within our Veeam Backup & Replication software, there is the ability to exclude files and folders from individual virtual machines, this feature is called BitLooker.
BitLooker enables the exclusion of swap file blocks from processing. Considering that each VM creates a swap file, which is usually at least 2 GB in size and changes daily, this is a considerable amount of data that noticeably affects full and incremental backup size. However, BitLooker automatically detects the swap file location and determines the blocks backing it in the corresponding VMDK. These blocks are then automatically excluded from processing, replaced with zeroed blocks in the target image and are not stored in a backup file or transferred to a replica image.
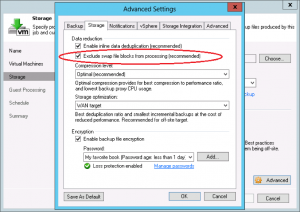
It is widely known that in many modern file systems deleted files do not disappear from the hard drive completely. The file will only be flagged as deleted in the file allocation table (FAT) of the file system (e.g., the master file table (MFT) in case of NTFS). However, the file’s data will continue to exist on the hard drive until it is overwritten by a new file. BitLooker Excludes these deleted files blocks from the backup set.
As well there may be certain files and directories that you don’t want to back up at all (e.g., application logs, application caches, temporary export files or user directories with personal files). There also might be data protection regulations in place that require you to exclude specific objects from backup. No longer do you simply need to accept the need to back up useless data with image-based backups.

This feature really does allow for a granular and selective approach to what is included in your backup jobs as well as being excluded on a retention period required.
The next topic we discussed was around suffering a data breach in the form of ransomware. Even more topical as it seems something around cybercrime is in the new each and every day at the moment.
What is Ransomware? I wrote a post on this a few months back as well as a recorded webinar that I will look to at the end.
“What is ransomware? – A type of malicious software (Malware) which restricts access to a computer and/or the files on a computer until a ransom amount is paid.
It’s something that is downloaded via email or file from the internet or passed between users much the same as a virus, this can be linked to a virus, malware, Trojan horse these are the same thing but a more evolved version.
What is it going to do to a single computer or network? – it’s going enforce restrictions through encryption and prohibit access to certain areas of a machine or an environment once infected.”
We discussed how Veeam cannot prevent the attack from taking place but it may be possible to assist in the recovery or getting to a stage before the attack took place. The post linked below goes into more detail on how you should be keeping your backup data in certain ways to prevent those backup files also getting infected with the spite of encryption that comes with a ransomware attack.
I also mentioned Veeam ONE and a new Monitor Alarm in there that can be useful in the detection of a Ransomware attack. This alarm uses some CPU and Disk monitoring to determine possible VMs that may be under attack and can notify the administrator of this. a fully tweakable alarm that may or may not just work in your environment.
The thresholds are:
For VMware VMs
* Average CPU usage is above 70.0% and datastore write rate is 40 MB/s for 5 minutes. – gives a warning
* Average CPU usage is above 80.0% and datastore write rate is 60 MB/s for 5 minutes. – gives an error
For Hyper-V VMs
* Total run time is above 70% and virtual storage write is above 40 MB/s for 5 minutes. – gives a warning
* Total run time is above 80% and virtual storage write is above 60 MB/s for 5 minutes. – gives an error
These numbers can be adjusted as well as virtual machines within your environment can be excluded if you know they would constantly be above that threshold. It’s really something there that can give more visibility and help the fight against Ransomware.
Information Commisioners Office (ICO)
RansomWARe – What is it good for? Absolutely nothing!
How Veeam can protect your business from Ransomware
If you want to hear more and you are heading to the IP Expo event in Manchester at the end of April then my session schedule is here.
